Following topics to be covered in this article are
- Introduction
- Conflicts with International Standards
- References (Check Here)
- Definitions
- Architecture
- Network Management
- Security
1. Introduction to Plant Network System
The purpose of this article document is to write a recommended methodology to provide proactive monitoring and alerting capabilities for Plant Networks and Computer Systems. These monitoring and alerting capabilities should provide plant network administrator(s) and technical support staff with semi-real time networks and systems security, health, performance and availability indicators for the purpose of prompt risk mitigation, detailed diagnostics and analysis. The intended users include engineers and / or technicians working as Process Automation Network (PAN).
4. Definitions used in this article are:
This section contains definitions for acronyms, abbreviations, words, and terms as they are used in this document.
Acronyms
DCS – Distributed Control System
ESD – Emergency Shutdown Systems
IP – Internet Protocol
ISA – The International Society of Automation
PCS – Process Control Systems
PAN – Process Automation Network
PMS – Power Monitoring System
SCADA – Supervisory Control and Data Acquisition
IP – Internet Protocol
TMS – Terminal Management System
VMS – Vibration Monitoring System
Abbreviations
Authentication: A security measure designed to establish the validity of a transmission, message, or originator, or a means of verifying an individual’s authorization to receive specific categories of information. When humans have assets that are worth to be protected, the authentication always exists. The initial step in protecting systems and information is authentication that identifies who.
What is Process Automation Systems (PAS): PAS include Networks and Systems hardware and software such as Process Automation Network (PAN), Distributed Control Systems (DCSs), Emergency Shutdown Systems (ESD), Programmable Logic Controllers (PLCs), Supervisory Control and Data Acquisition (SCADA) systems, Terminal Management Systems (TMS), networked electronic sensing systems, and monitoring (such as VMS AND PMS), diagnostic, and related industrial automation and control systems. PAS also include associated internal, human, network, or machine interfaces used to provide control, safety, maintenance, quality assurance, and other process operations functionalities to continuous, batch, discrete, and combined processes.
Logs: Files or prints of information in chronological order.
PAN: Process Automation Network, or sometimes referred to as Plant Information Network (PIN), is a plant-wide network (switches, routers, firewalls, computers, etc. interconnecting process control system and provides an interface to the corporate network. PAN Administrator: Process Automation Networks (PAN) Administrator administers and performs system configuration and monitoring and coordinating with Process Control System Administrator, if different, as designated by the plant management. The PAN Administrator assumes the ownership of the IA&CS including the PAN Firewall and has the function of granting, revoking, and tracking access privileges and communications of users on IA&CS including the Firewall.
Password: A form of secret authentication data that is used to control access to a resource. Password authentication determines authenticity based on testing for a device or a user that is requesting access to systems using for example a personal identification number (PIN) or password. Password authentication scheme is the simplest and most common mechanism.
Server: A dedicated un-manned data provider.
5. Plant Network Architecture
5.1 Plant Network Systems Components
5.1.1 Hardware
The monitoring and alerting appliance may utilize a standard server hardware configuration that can be procured separately from the software provided by the monitoring appliance vendor. The appliance may also be based on a proprietary hardware tightly integrated to the software provided by the monitoring appliance vendor.
There is no specific preference in selecting either hardware option, as both alternatives have prevalent pros and cons.
5.1.2 Software
Server: The monitoring and alerting appliance is typically configured on top of Windows®, operating system; however, other operating systems such as IBM AIX®, Solaris and Linux® are also supported. This is true for both standard server hardware configuration, and a server based on a proprietary hardware tightly integrated to the software provided by the monitoring appliance vendor.
The PAN administrator shall NOT attempt to connect monitoring and alerting hardware components directly onto critical networks such DCS, SCADA LAN or ESD without a prior approval from vendor, as this could cause a conflict or performance issue with the DCS hardware.
Client: The monitoring and alerting appliance does not usually require installing a client application on remote systems (front end) in order to convey monitoring and alerting information to the server. In fact, PAN administrator shall NOT attempt to install any additional software or alter configuration on critical Process Control systems without a prior vendor certification for this application as this is critical to maximize PAS uptime and ensure vendor PAS support.
There is no specific preference in selecting either hardware option, as both alternatives have prevalent pros and cons.
5.1.3 External Interfaces (Peripherals)
The monitoring and alerting appliance should support a minimum number of peripherals such as Environmental Sensors, GSM modems, email interfaces, etc. These peripherals provide additional monitoring parameters such as room and rack temperature levels, humidity and floods…etc.
Other peripherals provide advanced alerting mechanism such as paging and email notification.
– USB ports for environmental sensors or GSM modem
– USB enabled devices (mouse, keyboard)
– Power on/off button.
– PS2 port for Keyboard
– VGA port to attach a cable to a display
– RJ45 port for Ethernet cable (10/100/1000)
5.2 Plant Network System’s Requirements
An effective monitoring and alerting tool shall be capable to provide and/or support monitoring functions such as:
5.2.1 Performance and Availability Parameters
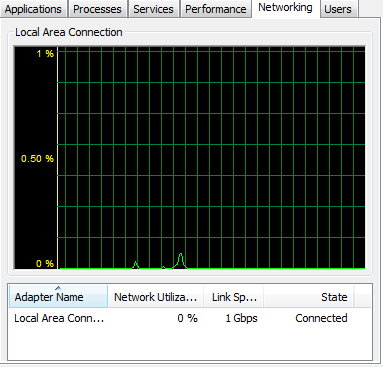
Systems CPU / Memory utilization (Figure 1)
Systems hard drive capacity and utilization (Figure 2)
Processes – running processes, systems resources utilized
Network – availability, utilization, TCP/UDP ports information (Figure 3)


5.2.2 Security Parameters
Account Policies – accounts that are Locked, Unused or Invalid
Antivirus Software – Version, update and scan history
System Services – Running Services, Stopped Services, etc.
Registry – key search
Logs – event monitoring
5.2.3 Notifications Options
Email – the ability to send notifications using Simple Mail Transfer Protocol (SMTP) within the PAN.
Text Messaging – the ability to send text based messaging through the operating system or applicationPaging – is specially important during network or system downtime. When a problem is detected, the Monitoring and Alerting appliance shall be able to page the PAN administrator(s) via cell phone text messages (SMS), e-mail, MSN, etc. Some can even take corrective actions by restarting a server or service. Alerts can be sent to multiple people in different ways depending on day of the week and time of the day.
5.2.4 Application Specific Alerts and Reporting
Email – important with Line of Business Applications (LOB). The monitoring system should have the intelligence to watch for applications-specific event log messages.
5.2.5 System Redundancy
The monitoring tool is based on a redundant hardware to maximize availability of the system. Redundancy is best achieved if selected hardware supports a dynamic databases replication and failover mechanism. Otherwise, fully configured independent systems can be installed to provide the required redundancy. This option however, will require manual synchronization and intervention in case of system failure.
5.3 Plant Network Parameters
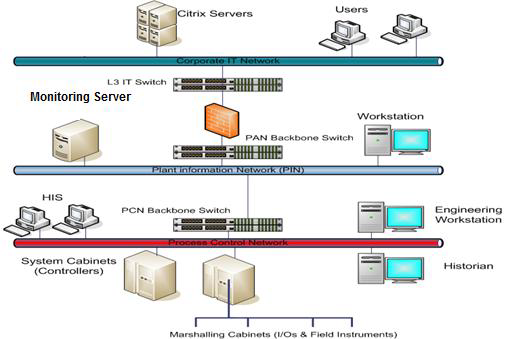
The redundant hardware shall be connected respectively to Plant’s redundant PAN backbone switches. To monitor private networks such as DCS or ESD networks, a proxy system conveying performance management information can be also be installed using a dual homed configuration. See Figure 4.
5.3.1 IP Addressing
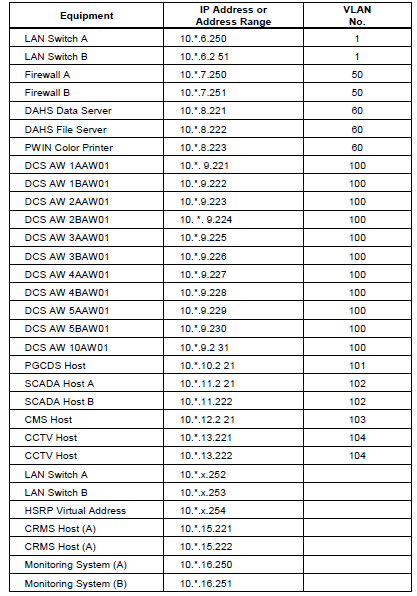
A list of network IP addresses of all systems to be monitored shall be are obtained and kept in table such as the one below:
5.3.2 SNMP
The other alternative is to install Simple Network Management Protocol (SNMP) on each system as a mechanism to provide system performance information such as CPU and Memory utilization, etc. However, this option requires reconfiguration of all systems at stake with SNMP v3, at minimum, along with the right community strings for PUBLIC and PRIVATE parameters, a process seen cumbersome, yet possible, if so chosen.
5.4 Systems Parameters
5.4.1 Access Privileges
In order for the monitoring system to be able to query other systems, it may require to have an administrative user credentials on each system to be monitored. Equivalent rights to the “Administrator / Root” accounts may be assigned to the monitoring systems to allow it perform systems and logs inquiries.
Some monitoring systems are configured with an internal account that has to match a respective account in each system to be monitored with administrative privileges.
6. Plant Network Management
6.1 Device Management
The Monitoring and Alerting System is accessible through:
1. Web-browser interface
The Monitoring and Alerting System is accessible through a standard web-based browser utilizing the Hyper Text Transfer Protocol (HTTP) and a pre-determined TCP port. This methodology provides broader convenience and ease of use as this provides the ability for the Monitoring and Alerting appliance to be managed from fixed computers, laptops or hand-held devices. A special consideration shall be observed when using HTTP, as contents in this protocol are exposed in clear text. For that reason, the Monitoring and Alerting system shall support Secure HTTP (HTTPS) or SSH for device management for better security and confidentiality.
2. Front-end application (Client Server)
Alternatively, the Monitoring and Alerting System can be accessible through a front-end, an associated vendor-based application part of the “Client / Server” model. This approach is fairly safe and provides full management capability to the Monitoring and Alerting appliance; however, the appliance can only be accessed from computers that are pre-installed with the client. A special consideration shall be observed when using this model with regard to licenses, client minimum hardware and software requirements.
6.2 Network Traffic Considerations
The Process Control network is a mission critical network, thus, a certain level of delicacy must be observed when adding a new system or device onto the network. The selected Monitoring and Alerting system shall not exhibit an intrusive behavior burdening the network with unnecessary and frequent requests.
The Process Monitoring and Alerting System shall be configured to minimize the polling cycle to reduce unnecessary strain on both the monitored device and the network. The threshold for system resources devoted to provide the required monitoring information must be carefully calculated by the PAN administrator(s) and concurred upon by the respective Process Control vendor to ensure over all availability and stability of both the monitored device and the network.
7. Plant Network Security
7.1 Device Security
Access security for the Monitoring and Alerting System is implemented by means of configuring User and Administrator names and passwords on each server / client connected the system. The PAN Administrator(s) create and modify all user names and passwords for the PAN and maintain this configuration following the mandatory requirements as per SAEP-99 “Process Automation Networks and Systems Security”.
The location of the Monitoring and Alerting system shall be carefully selected with special consideration to both network and physical security requirements. The selected location of the appliance must adhere to the “Physical Security” requirements specified in SAEP-99, specially those pertaining to asset tagging, labeling and locked cabinets.
In addition to the security of the device itself, some Monitoring and Alerting systems can provide physical security monitoring for other devices in the server room or data center. Special security sensors (occupancy sensors) can be used to monitor your racks or computer room to alert the PAN administrators(s) when intrusion is detected. It can automatically record series of snapshots by retrieving and storing images captured from a camera specially mounted for this purpose.
7.2 Network Security
7.2.1 Information Security
The information gathered by the Monitoring and Alerting appliance and passed over the network must be classified by the plant management in accordance to GI-0710.002 “Classification of Sensitive Information”, by which the following shall be considered:
Classified information passing through general business network shall be encrypted.
Access to classified information shall be closely controlled and monitored.
If the Monitoring and Alerting appliance is maintained and operated by another organization, appropriate Server Level Agreement shall be in place.
7.2.2 Remote Access
Remote Access capabilities can bring about considerable cost savings and operational convenience to plant organizations with geographically scattered sites installations. Needless to mention that potential security risks are traditionally associated with remote access capabilities, and the following guidelines must be considered:
Remote Access shall be established utilizing the existing corporate proxy server setup (Citrix Metaframe), or server-to-server methodology as per SAES-Z-010 “Process Automation Networks” standard.
Appropriate level of security must be established on the Remote server, this includes measures such as:
– Latest version of company supported antivirus software and virus signature data file.
– Latest updates of Operating system patches and hot fixes.